Objective 5.1 – Backup and Restore Network Configurations
Skills and Abilities
- Schedule/Backup/Restore NSX Manager data
- Export/Restore vSphere Distributed Switch configuration
- Export/Import Service Composer profiles
- Save/Export/Import/Load Distributed Firewall configurations
Schedule/Backup/Restore NSX Manager data
Having backups of your NSX environment is highly recommended in case you ever need to restore your config back to a working state in the event of a failure. A NSX backup will contain all of the NSX configuration, including controllers, logical switches, logical routers, firewall rules and other things that were configured within NSX. It is also good to have the vCenter database and distributed switch configs backed up so that you have a complete recovery point.
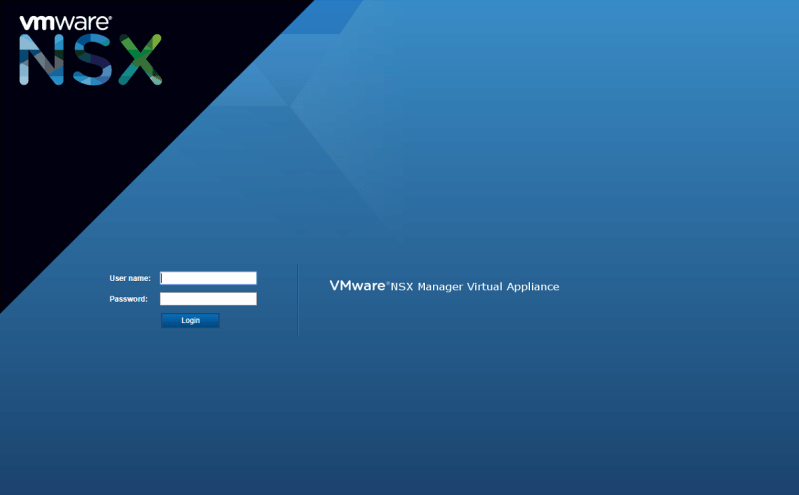
To begin setting up the backup, log in to the NSX Manager.