The NSX service composer is one of my favorite features of NSX. I’ve never really considered myself to be lazy when it comes to doing something the right way…but I’ve never been one to overwork myself to do that. Dad always said “Work smarter, not harder”. The service composer is a combination of both. It’s a way to create multiple rules in your virtual infrastructure for items that are alike or that need to have the same type of services allowed or denied. For you Cisco guys, this is a familiar concept. Think objects and object groups on a ASA. For example, say I have a group of 6 web servers that I want to block ICMP traffic. Well that would normally mean that I would have to create 6 individual rules, one for each web server, to block this. With the service composer, however, I can create one rule. With the use of security groups and security policies, service composer makes life easy…and that doesn’t mean that you’re lazy 🙂
In this blog post, I will show you how to use the service composer to create a security policy and apply it to multiple servers.
First navigate to Networking & Security > Service Composer
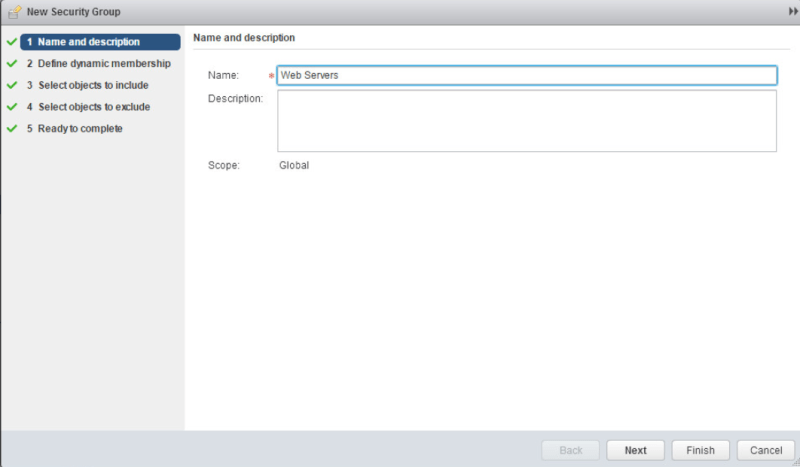
The first tab that we are presented with is the Security Groups tab. Security groups are the actual assets that you want to protect. Once again, Cisco guys, think object groups. We will create a new security group for our webs servers. Click the new security group button. Enter a name for the security group. Click Next.
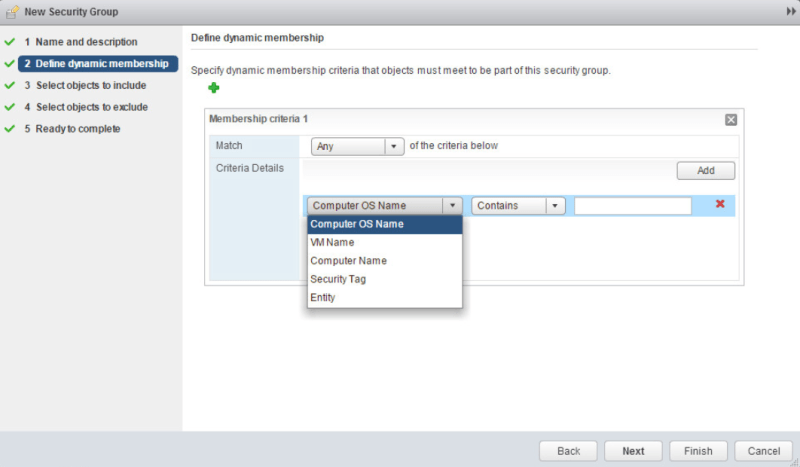
Security groups can have both dynamic and static memberships. With static memberships you define specific VMs that you want to protect. With dynamic memberships, VMs can be defined based off a certain criteria that you set. Also with dynamic memberships, new VMs will be added automatically if they meet the criteria that is set.
For our web servers, the criteria will be VM Name containing the word “web”. Click Next.
Here is where we can define static memberships. If your security group is not going to change much or at all, then create a static security group membership. Click Next.

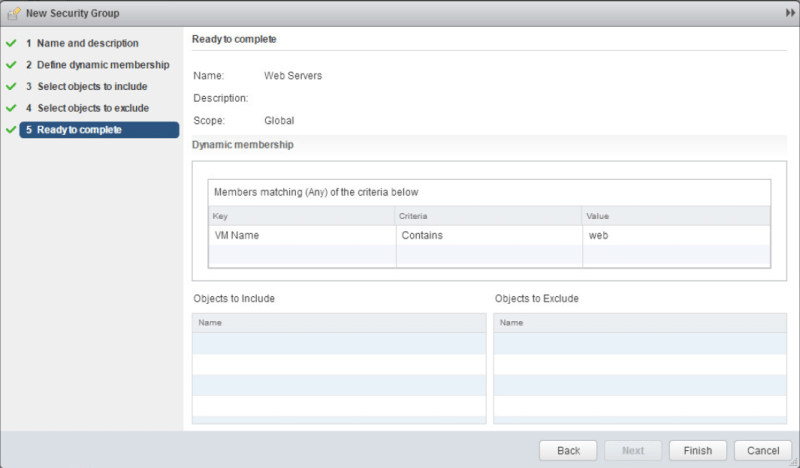
This screen show the exclusion list. If we have VMs that we would not want to be a part of our security group, they would go here. Click Next.

Click Finish.
Notice our newly created security group
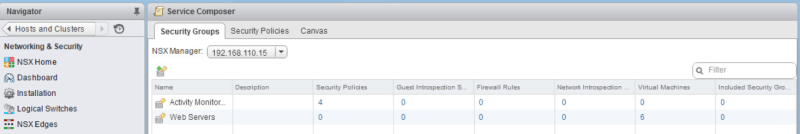
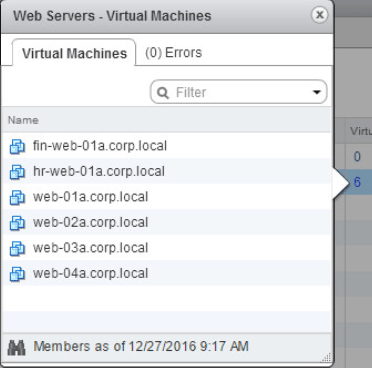
Under the Virtual Machines column, there is a number. If we click that number, it will show us what VMs are a part of our group.
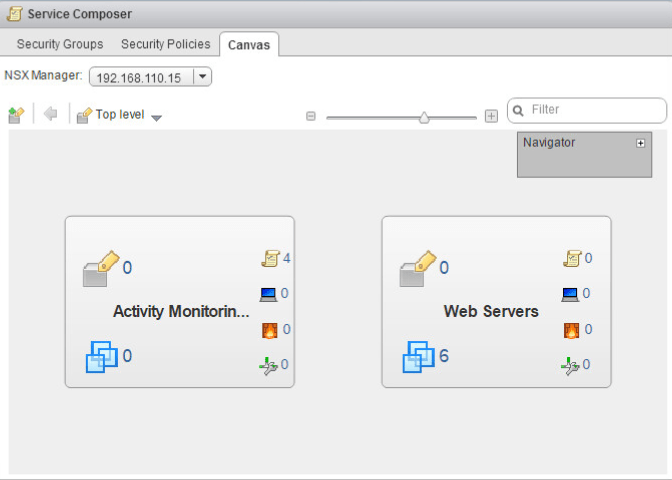
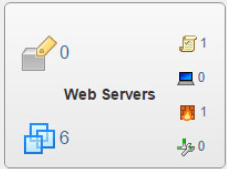
Notice under the Canvas tab, we now have a canvas object for the Web Servers security group that we just created.
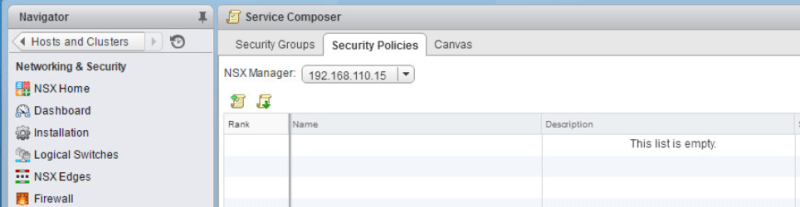
Navigate to the Security Policies tab. Click New Security Policy button.
Enter a name for the security policy. Also notice under the advanced options, there’s number under Weight. This is used when you have multiple security policies. The policy with the higher number has higher precedence. Click Next.

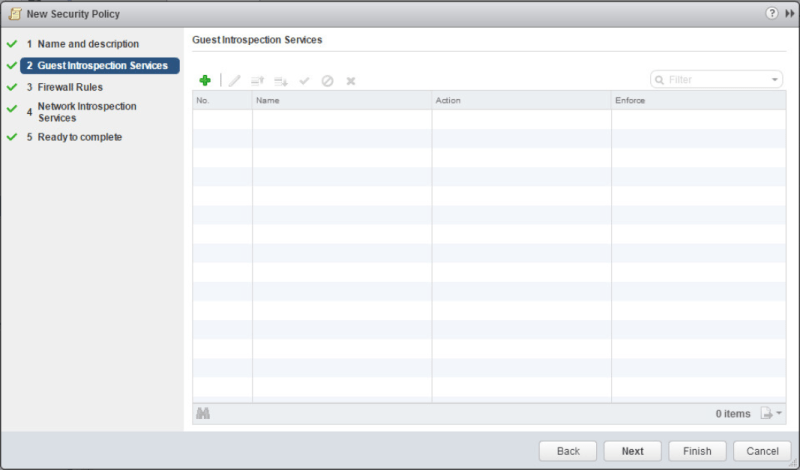
Click Next on the Guest Introspection Services page
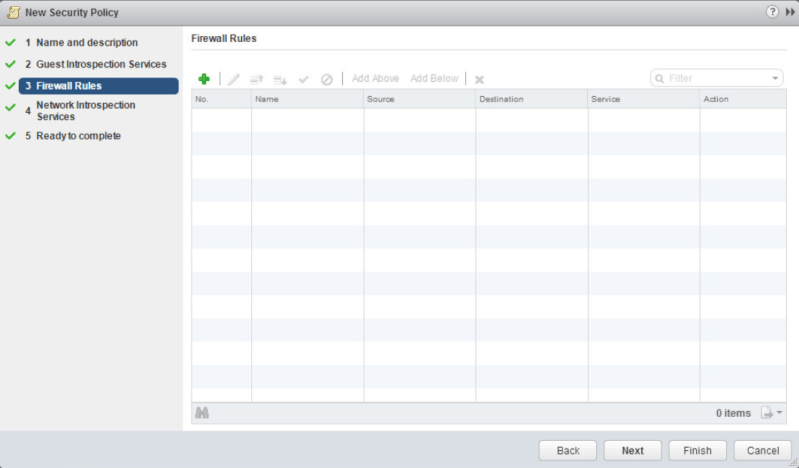
Click the green + on the Firewall Rules page
Here is where we define our firewall policy. Enter in a name for the rule and next to Action, select Block. Next to Service click Change.
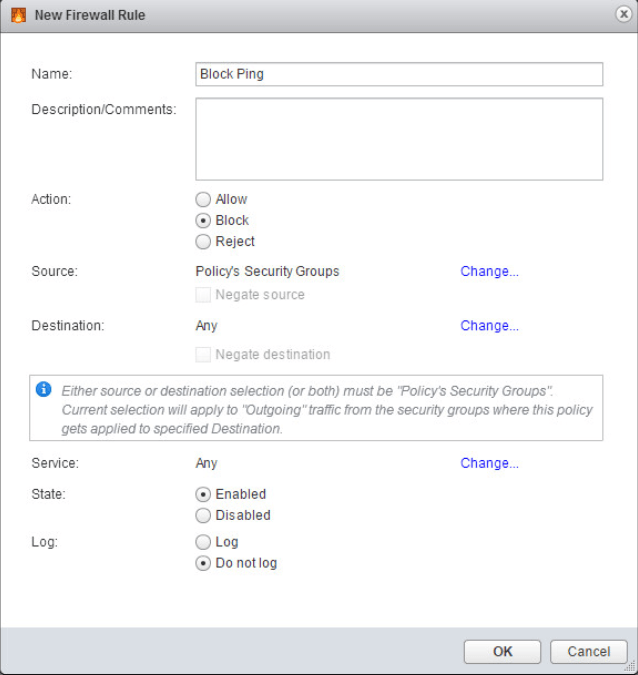
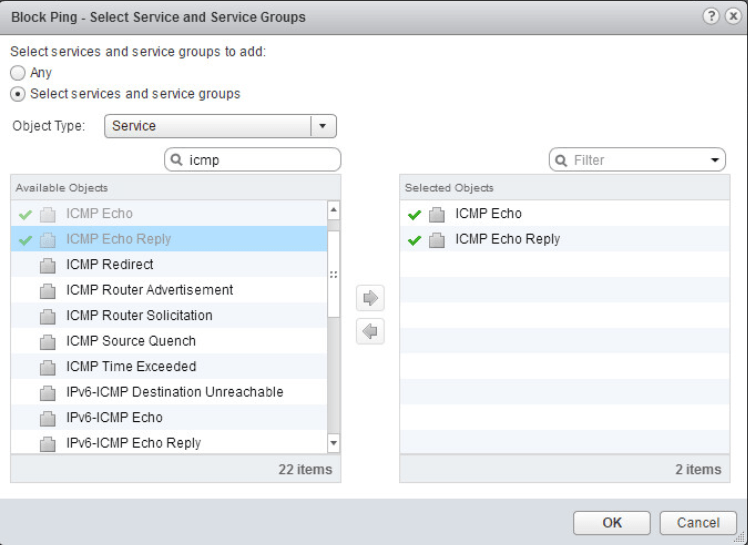
Here is where you define what services you want to allow or block. In our case we just want to block ICMP. So search for icmp and double click ICMP Echo and ICMP Echo Reply. Click OK.
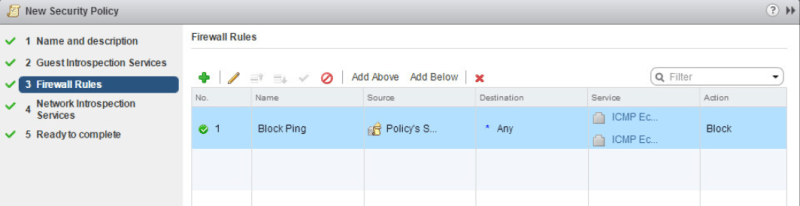
Now we have our firewall rule created. Click Next.
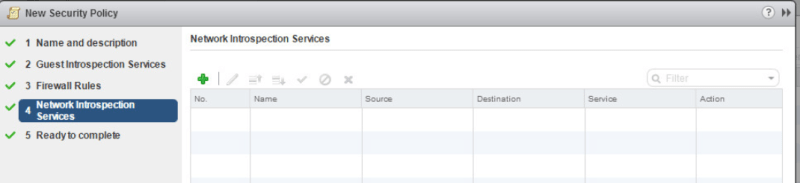
Click Next on the Network Introspection Services page.
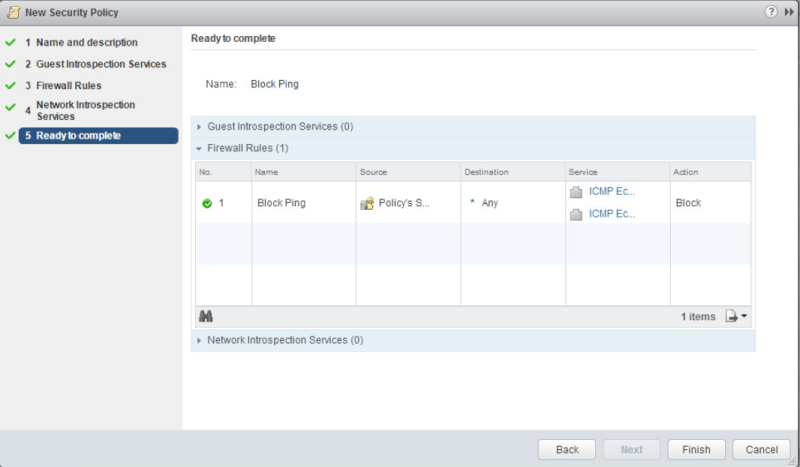
Verify that all of our settings are correct and click Finish.
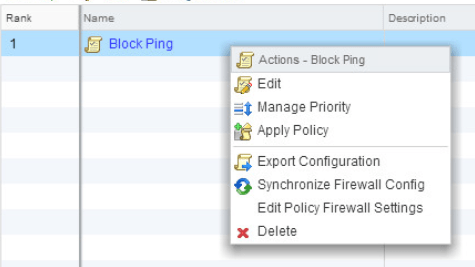
Now under the security policies tab we will see our newly created policy

Now we need to apply the security policy to the security group that we created earlier. Right click the security policy and select Apply Policy
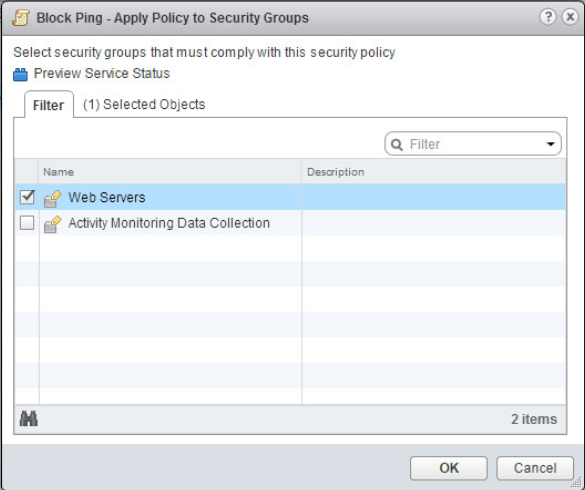
Select the Web Servers security group that we created. Click OK.
Now if we navigate over to the Canvas tab, we will see that our Web Servers canvas object has a security policy and a firewall rule associated with it. Only thing left to do is to test our firewall rule.
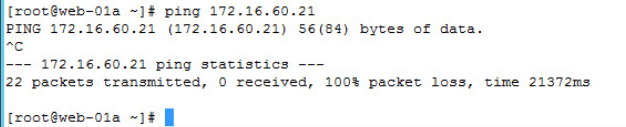
Here are the ping results from one of my web servers that is a part of the Web Servers security group.
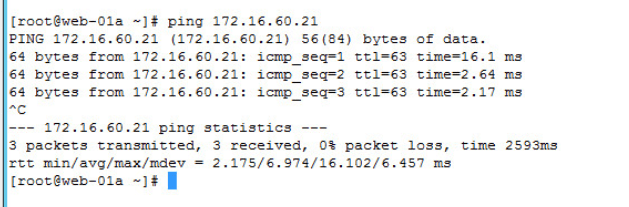
Here’s the output for the ping results after removing the security policy from the security group.
That’s it! Now can’t you see how simple and efficient it is to use the service composer to create security groups and security policies for VMs rather than creating individual firewall rules for each VM? So “work smarter, not harder”.